Kaspersky Malware Reverse Engineering And Analysis

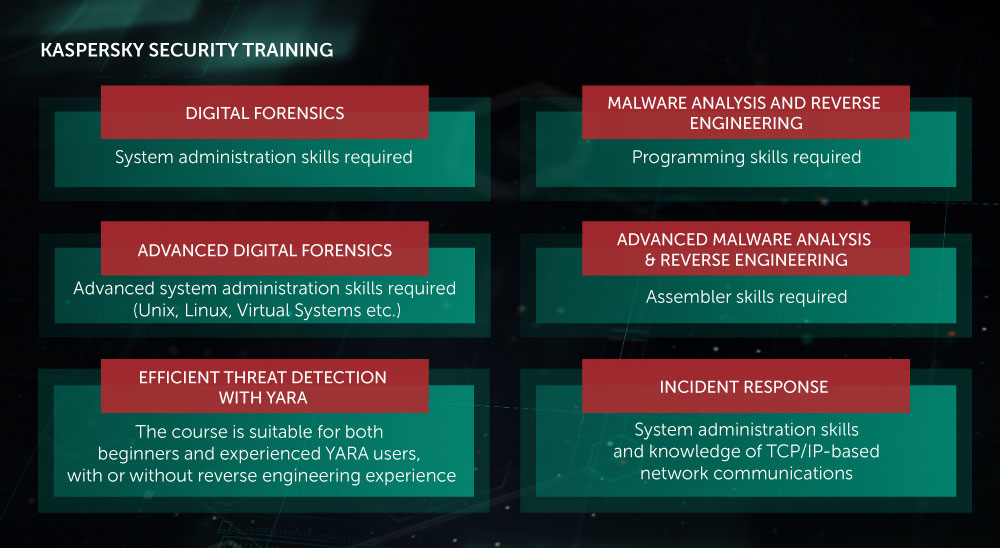
LEVELS 2-3 Malware Analysis Reverse Engineering Improve the expertise of your in-house malware analysis and reverse engineering team.
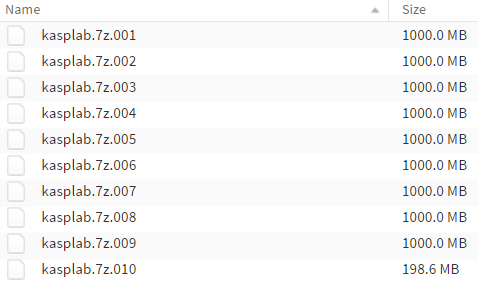
Kaspersky malware reverse engineering and analysis. You can use 7zip also in windows or linux. This course is meant as a practical course on malware reverse engineering and analysis for beginners. Kaspersky Lab - Malware Analysis Reverse Engineering Kaspersky Security Training - lectures and labs - 5 days - volume - 10-14 licenses Manufacturer.
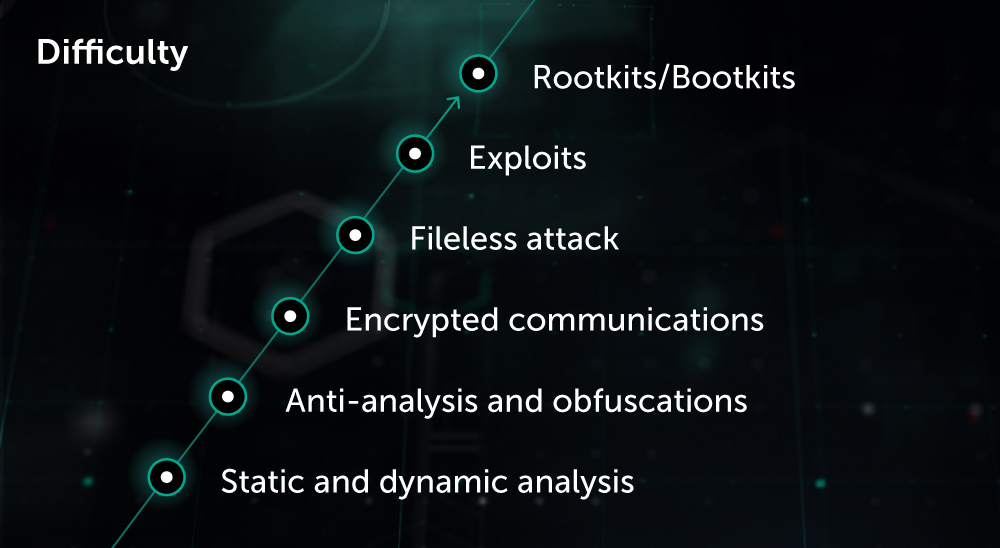
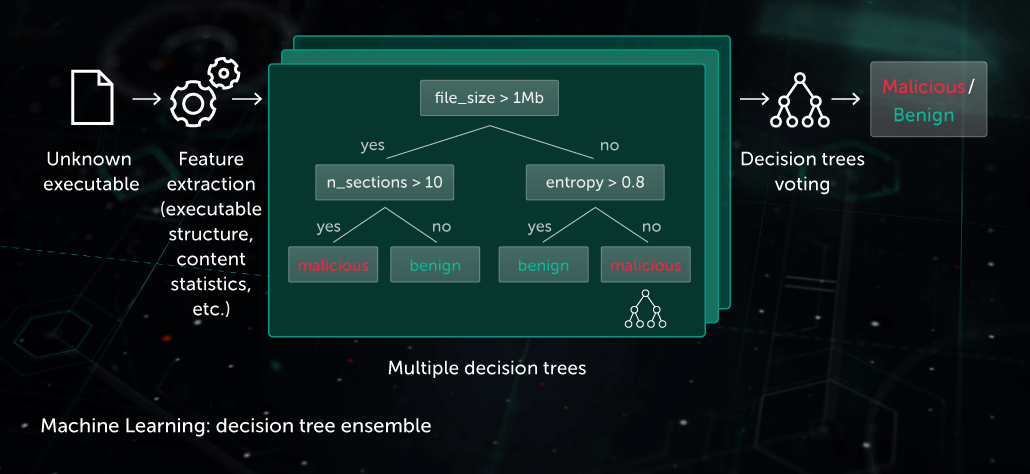
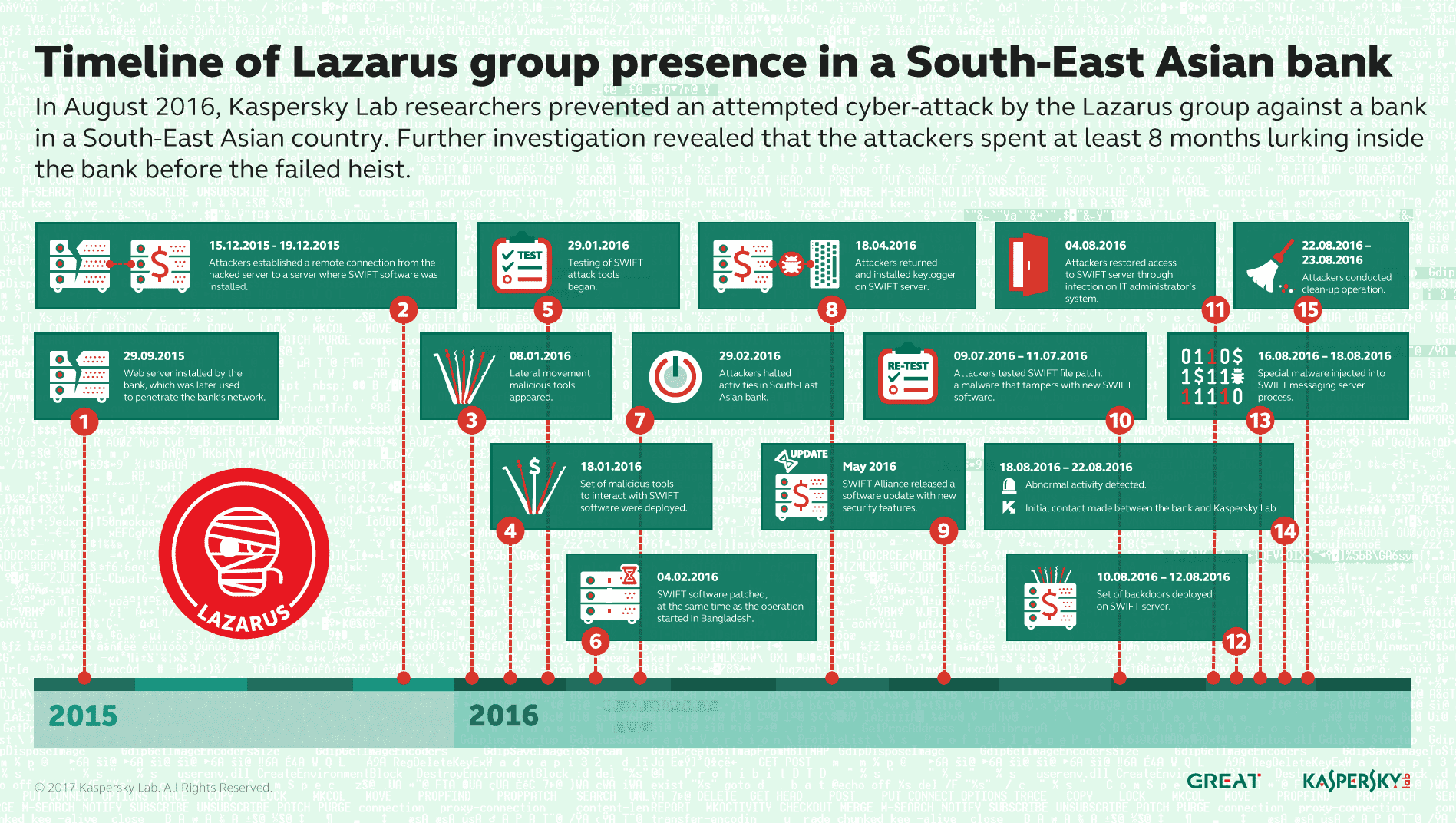
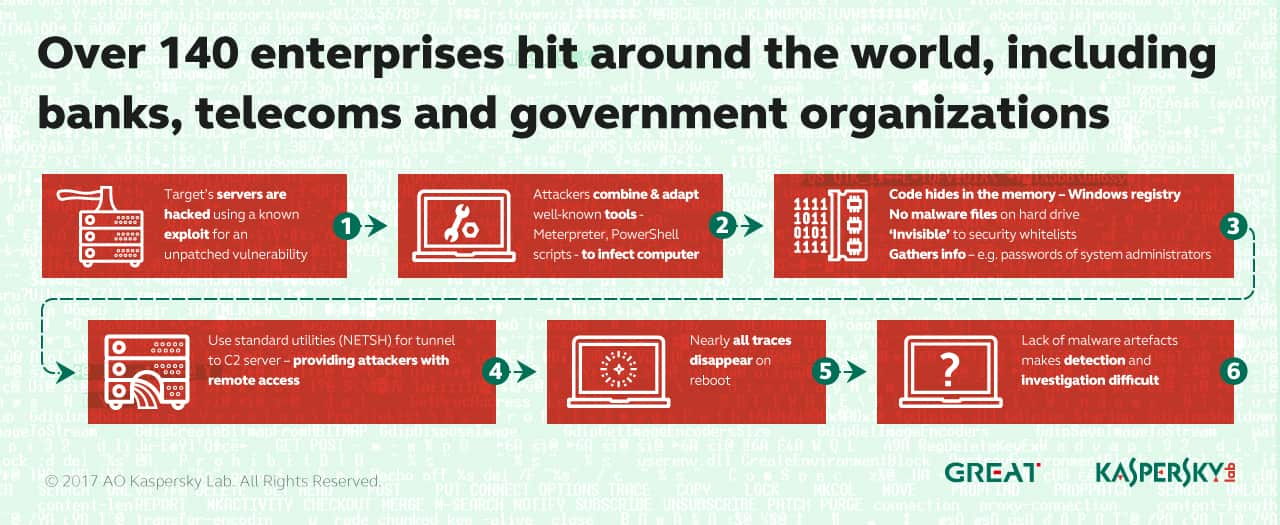
FOR610 training has helped forensic investigators incident responders security engineers and IT administrators acquire the practical skills to examine malicious programs that target and infect Windows systems. Our experts understand how best to handle the threats posed. In order to prevent the reverse engineering of a malicious software program and to hinder the analysis of the programs behaviour malware developers may compress or pack their malicious programs using a variety of methods combined with file encryption.
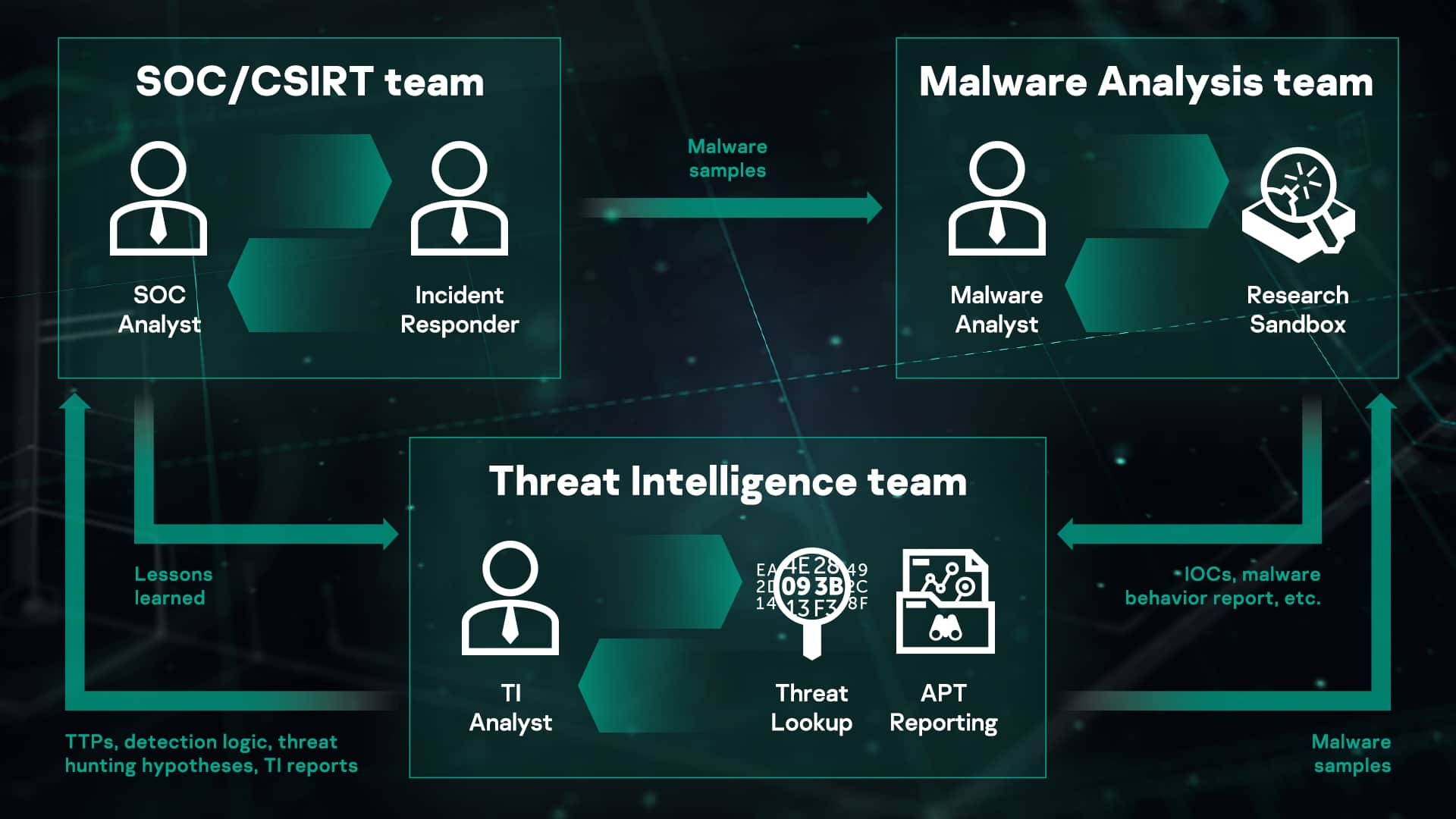
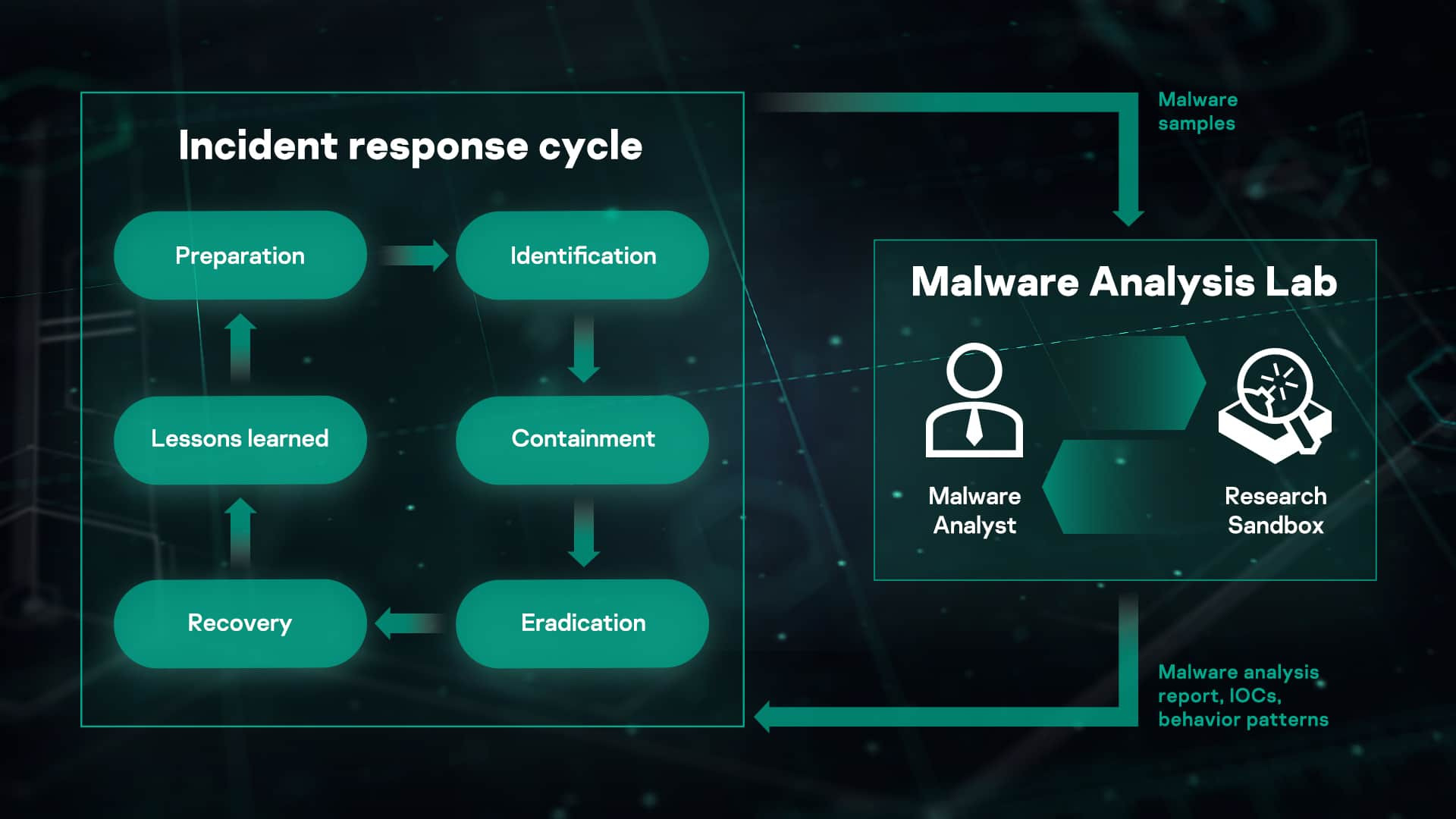
And Advanced Malware Analysis and Reverse Engineering These courses are intended for security researchers and incident response personnel malware analysts security engineers network security analysts APT hunters and IT security staff. Students will learn to analyze malicious software to collect IoCs Indicators of Compromise to write signatures for detecting malware on infected machines and to restore infectedencrypted files and documents. This course is intended for IT department employees and system administrators.
Kaspersky Lab Part. Become familiar with the scope of reverse engineering applications assembly language corresponding tools and the techniques used by malware authors to cause damage. Malware Analysis Reverse Engineering.
Nowadays Chebyshev is an experienced specialist and has deep knowledge in Android Linux and Mac OS malware. Within this role he acquired great experience in reverse engineering and software development. By 2013 he was promoted to Non-Windows Malware Research Group Manager and then at 2015 to Security Expert.
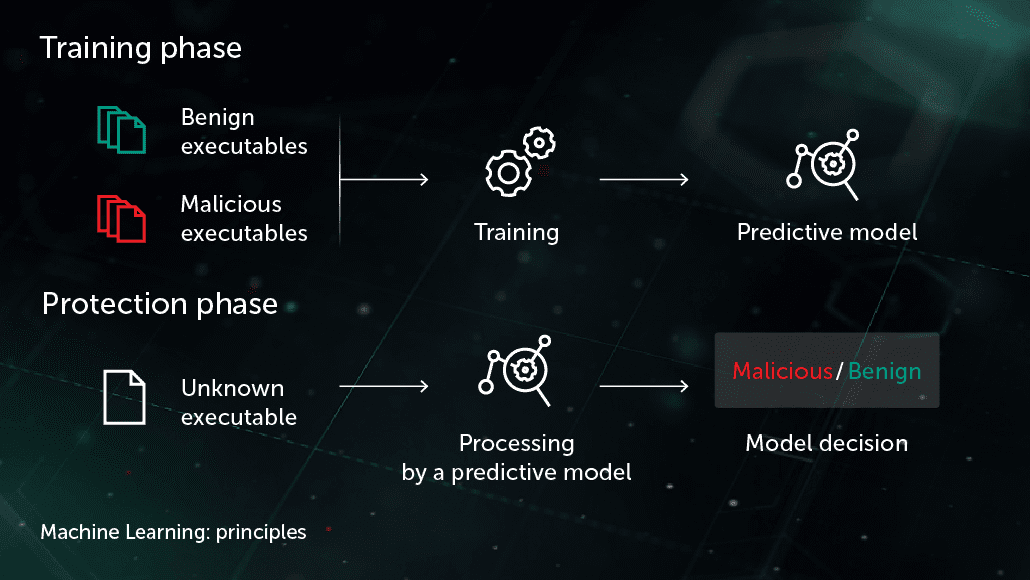
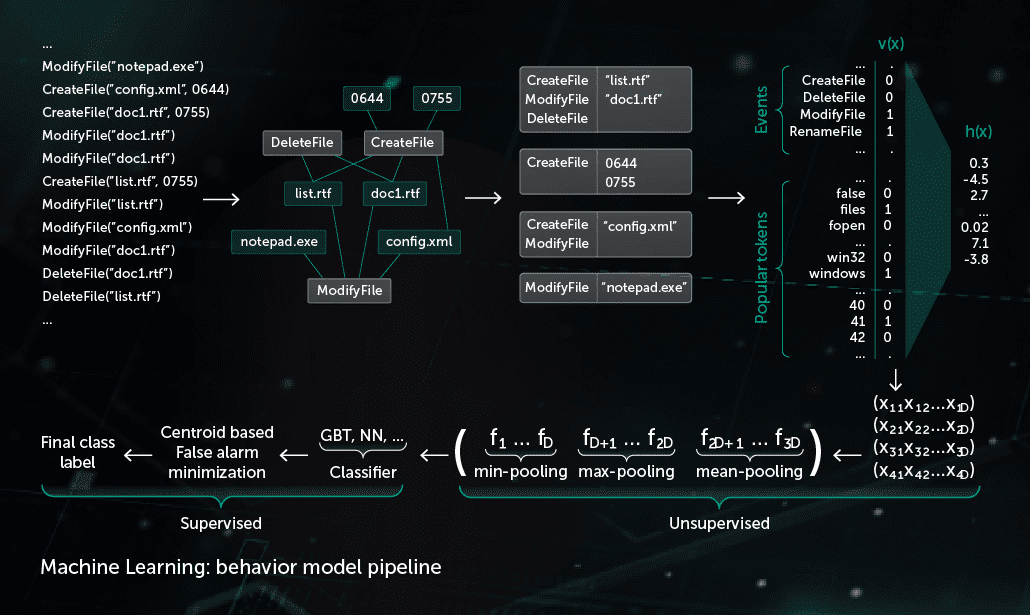
Dynamic malware analysis tools observe the behavior of the malware while it is running as a host program. I think you have to rename it like example kasplab7z001 kasplab0017z do this to every file and try to unarchive using winrar. This course is written by Udemys very popular author Abhinav singh.